Our internal CTI platform gives security teams, researchers, and law enforcement a structured environment to scan, investigate, and hunt threats — backed by Karen IT's own data collection infrastructure, threat feeds, and image clustering technology.
When a suspicious URL surfaces — in a phishing report, an incident, a threat feed, or an investigation — most tools give you surface-level answers. Our CTI platform goes deeper.
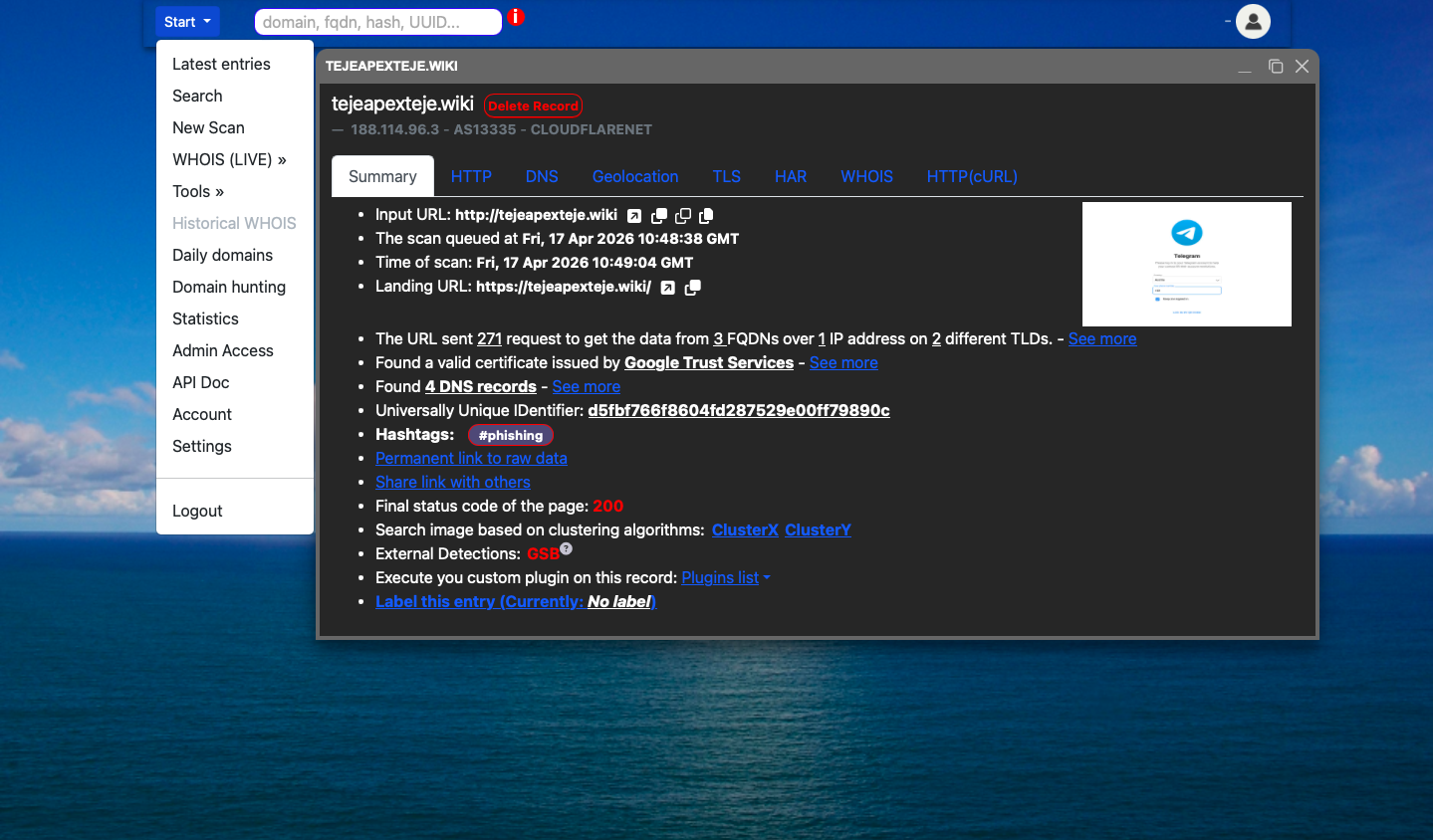
A single scan returns the full technical stack: HTTP behavior, DNS records, TLS certificate details, geolocation, WHOIS data, HAR interaction logs, favicon hashing, and image-based clustering — all in one structured, queryable record.
Every scan is permanently linked, exportable as raw JSON, and searchable across dozens of fields. Built for analysts who need answers fast, and for investigations that require documentation that holds up.
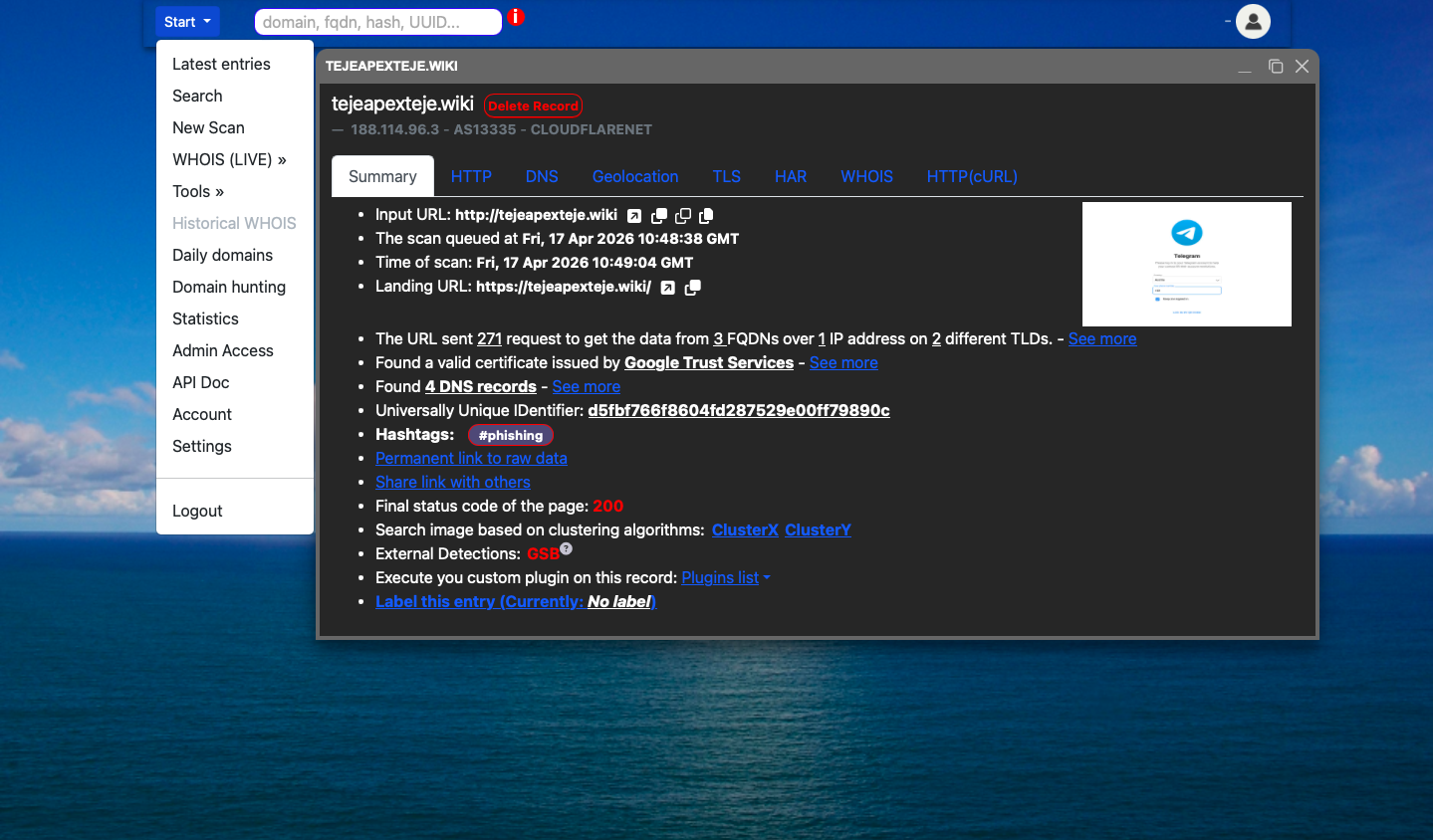
Each scan produces a structured record across eight data layers. Private scan mode is available for sensitive investigations.
The top-level overview of every scan — everything you need at a glance, with links to deeper layers.
The browser-level rendering of the page — what a real browser sees when it loads the URL.
DNS resolution data collected using public resolvers (1.1.1.1, 8.8.8.8). Responses follow RFC 1035.
Network-level location mapping for every IP address encountered during the scan.
Full certificate inspection for the landing domain — issuer, validity window, fingerprints, and all covered names.
The complete log of browser interaction with the target website. Every request made by the browser, captured in full.
Domain registration data from public WHOIS records — registrar details, dates, and nameserver information.
Raw HTTP-level inspection — separate from browser rendering. Captures what the server actually sends, without JavaScript execution.
Build single-field lookups or construct compound rules with AND/OR logic across any combination of fields. Export results for use in your own workflow or SIEM.
.xyz AND ASN = 12345 AND WHOIS creation date > 2024-01-01.Every tool in the platform is designed around a real investigative workflow — not a feature checklist.
Find visually similar pages across all scans in the database. Our platform captures screenshots of every scanned URL and clusters them using two independent algorithms. Effective for identifying phishing kit reuse — the same template deployed across dozens of unrelated domains.
When a threat actor registers one malicious domain, the probability of several others registered simultaneously is high. Domain Hunting surfaces domains sharing registration patterns, naming conventions, or structural similarity with a known malicious domain.
Browse newly registered domains by date and TLD. Useful for early detection of typosquatting, brand impersonation, and infrastructure preparation by threat actors — before the domains are activated for an attack.
Full web-based dig command-line interface. Query any domain's DNS records directly through the platform — no command line required. Useful for quick DNS lookups during an investigation without leaving the platform environment.
Real-time WHOIS lookup for both domains and IP addresses. Domain WHOIS returns registrar, dates, nameservers, and registrant data. IP WHOIS returns ASN, network range, organization, and country.
The Latest Entries view displays recently scanned URLs in real time. Visibility is governed by your role and permissions. The feed refreshes automatically every 5 minutes — useful for coordinating team-wide investigations and spotting emerging clusters.
All platform capabilities are accessible programmatically. Integrate scan submission, result retrieval, and search queries directly into your SIEM, automation pipelines, or custom tooling.
Full API documentation is available to authorized users. Rate limits and access tiers are defined per-organization based on your use case.
Request API AccessAccess to the Karen IT CTI platform is provided to vetted organizations and individuals operating in a security capacity. This is not a public tool.
Access requests are reviewed individually. If your organization has a legitimate security or investigative need, contact us to discuss access terms and integration requirements.
Our CTI platform is built around one principle: give analysts the full picture, fast, in a format they can use. Whether you are triaging a phishing report, hunting a threat actor's infrastructure, or building evidence for a law enforcement referral — the platform is designed to support that work.